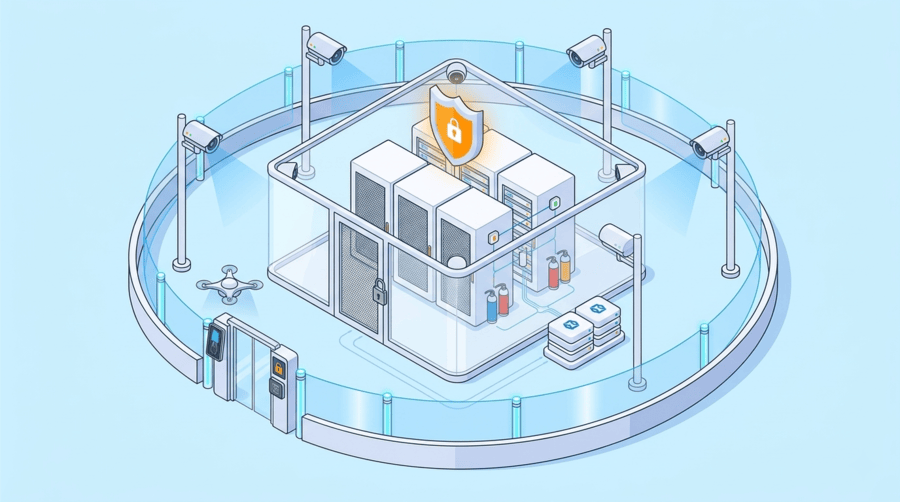
A data center can have strong cybersecurity controls and still face serious exposure if its physical defenses are inconsistent. In real environments, risk often appears in the transition points: a perimeter that is visible but not well monitored, a visitor process that exists on paper but is loosely enforced, or a data hall with controlled entry but limited rack accountability. Once critical systems are running inside the facility, those gaps become harder to correct without disruption.
That is why physical security layers in modern data centers matter. A layered approach helps operators deter threats early, verify identity at multiple points, control movement inside sensitive areas, and protect infrastructure from both intrusion and operational incidents.
Why layered physical security matters
Good data center physical security follows a defense-in-depth model. If one control fails, the next control reduces the chance of a full breach. This is the foundation of physical security in data centers across enterprise, hyperscale, and colocation environments.
The goal is not to add unnecessary complexity. It is to make access harder to abuse, easier to audit, and faster to investigate.
Tip for dedicated server buyers: Ask whether the provider can explain the full security flow from the property boundary to the rack. If they only mention the building entrance, that is not the full picture.
-
Perimeter security
The first layer begins outside the facility. This usually includes fencing, gates, bollards, security lighting, perimeter sensors, and exterior camera coverage. Larger sites may also use thermal cameras, license plate recognition, or on-site patrols.
This layer is designed to deter casual intrusion, detect suspicious activity early, and create response time before someone reaches the building.
Note for dedicated server buyers: A strong perimeter reduces the chance that threats get close enough to test the inner layers.
-
Guardhouse and visitor screening
Before entering the building, visitors should pass through a controlled approval process. This can include pre-registration, sponsor approval, identity verification, and in some cases screening of carried items.
This stage matters because third-party visitors, contractors, and short-term vendors often create the most variation in physical access routines. A structured process reduces that risk.
Tip for dedicated server buyers: Ask how visitors are approved, logged, and restricted. Good security is not only about staff access, but also about how temporary access is handled.
-
Building entry and access control
Once at the entrance, identity verification becomes stricter. This is where data center access control plays a central role. Common controls include staffed reception points, access badges, biometric checks, and mantraps to reduce tailgating.
The objective is to make sure only authorized people enter, and that every entry event is tied to a known identity and valid purpose.
Note for dedicated server buyers: If access relies only on a badge and not stronger checks such as biometrics or monitored entry, the control may be weaker than it sounds.
-
Internal zoning
Being allowed into the building should not mean being allowed everywhere inside it. Modern data center security layers usually divide the site into separate zones such as office areas, support rooms, loading areas, network rooms, and secure technical spaces.
This limits movement based on role and reduces unnecessary exposure to sensitive areas. It also helps contain insider risk.
Tip for dedicated server buyers: Ask whether the provider uses zone-based access, especially if your workloads require stronger separation from general facility traffic.
-
Lift or corridor access to secure areas
In larger or multi-floor facilities, another layer often appears between general building access and the data hall. This may involve controlled lift access, secure corridors, anti-tailgating sensors, or monitored transition points.
This extra step helps ensure that people can only move toward the floors or rooms they have been approved to access.
Note for dedicated server buyers: Additional movement controls are useful because they prevent broad internal access after just one successful entry.
-
Data hall security
The data hall is where physical access risk becomes operational risk. Entry here is usually more restricted than at the main building entrance and may require extra authentication, monitored doors, and tighter surveillance.
This is an essential part of modern data center security layers because it protects the area where compute, storage, and network infrastructure are actually running.
Tip for dedicated server buyers: Ask how the provider controls and monitors access to the white space, not just the building itself.
-
Rack-level protection
The final physical layer is the cabinet or rack. Strong facilities use electronic rack locks, cabinet access logs, and sometimes biometric validation at the rack level. This helps create a clear record of who accessed what, and when.
This layer is especially important in colocation environments where multiple customers operate within the same facility.
Note for dedicated server buyers: If cabinet access cannot be traced clearly, accountability becomes much harder during audits or incident reviews.
-
Surveillance and monitoring
Data center surveillance systems support every layer above. Good surveillance includes internal and external CCTV, camera coverage aligned to doors and access points, and monitoring that helps teams verify events in real time.
The value is not just in recording footage. It is in linking visual evidence to access logs, alarms, and incident response workflows.
Tip for dedicated server buyers: Ask whether surveillance is actively monitored and whether footage can be tied back to access events if an issue occurs.
-
Environmental and operational safeguards
Physical protection is not only about unauthorized people. Fire detection, suppression systems, leak sensors, redundant cooling, backup power, and ongoing monitoring all protect the environment where infrastructure operates.
Operational discipline matters as well. Access reviews, staff training, testing, drills, and documented procedures help ensure those controls are consistently enforced.
Note for dedicated server buyers: A secure data center should be able to explain both the physical controls in place and the operational process behind them.
What this means for infrastructure buyers
If you are evaluating dedicated hosting or colocation, physical security should be part of the buying decision. It is worth asking how entry is controlled, how visitors are managed, how movement is restricted, how rack access is logged, and how incidents are reviewed.
For businesses that need dependable infrastructure in Hong Kong, Dataplugs provides dedicated server and hosting solutions backed by stable connectivity and professionally managed data center environments. This helps businesses support performance and operational reliability while keeping security standards strong in the background.
Conclusion
The main physical security layers in modern data centers include perimeter security, visitor screening, access control, internal zoning, secure movement paths, data hall controls, rack-level protection, surveillance, and environmental safeguards. Together, these controls help reduce risk, improve accountability, and protect critical infrastructure more effectively.
For dedicated server buyers, understanding these layers makes it easier to judge whether a provider is simply offering hardware space or a genuinely secure operating environment. To learn more, connect with Dataplugs via live chat or email at sales@dataplugs.com.