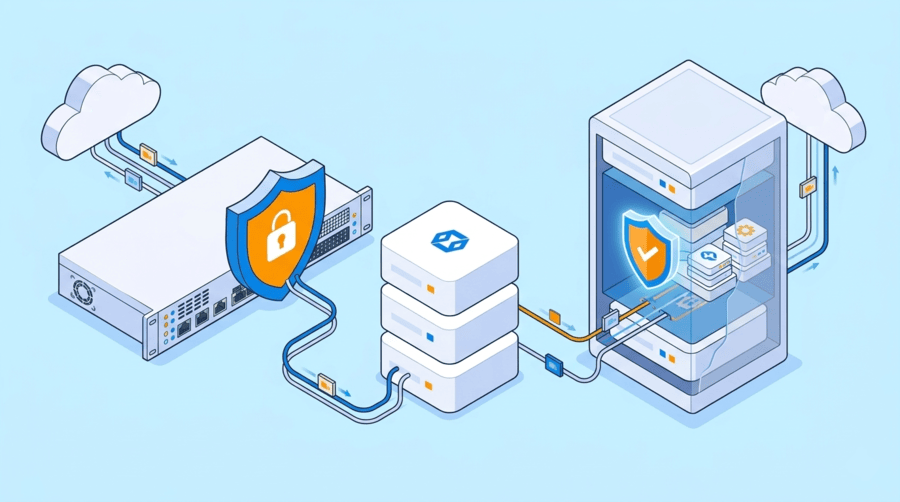
When you buy a dedicated server, firewall choice affects more than security alone. It also influences how traffic is filtered, how much load stays on the server, and how much control you have over access rules as the setup grows. That is why the difference between a hardware based firewall and a software firewall matters from the start.
For most buyers, the real question is not which firewall sounds better on paper. It is which one fits how the server will actually be used. A high traffic production server, a backend system, and a single app server will not need the same protection model.
What is a hardware firewall on a dedicated server?
A hardware firewall is a physical device placed at the network perimeter. It filters traffic before requests reach the dedicated server, so inspection happens outside the operating system and does not use the server’s own resources.
This setup is common in data center and enterprise environments because one device can apply rules across multiple systems. It also works well when larger traffic volumes need to be filtered without adding pressure to the server.
A hardware firewall dedicated server setup is often chosen for:
- public facing workloads
- multi server environments
- centralized security control
- high traffic applications
- stronger perimeter filtering
Because traffic is checked before it reaches the machine, this approach reduces direct exposure and keeps server resources focused on the workload.
What is a software firewall on a dedicated server?
A software firewall runs directly on the server. It is usually built into the operating system or managed through tools such as iptables, nftables, or Windows Firewall.
Instead of filtering traffic upstream, it controls traffic at host level. That gives administrators direct control over which ports, services, processes, or applications can communicate.
A software firewall dedicated server setup is commonly used for:
- single server deployments
- custom application environments
- direct OS level access control
- smaller scale infrastructure
- flexible rule management
For many businesses, this is the simplest firewall for dedicated servers because it can be deployed and changed without separate network hardware.
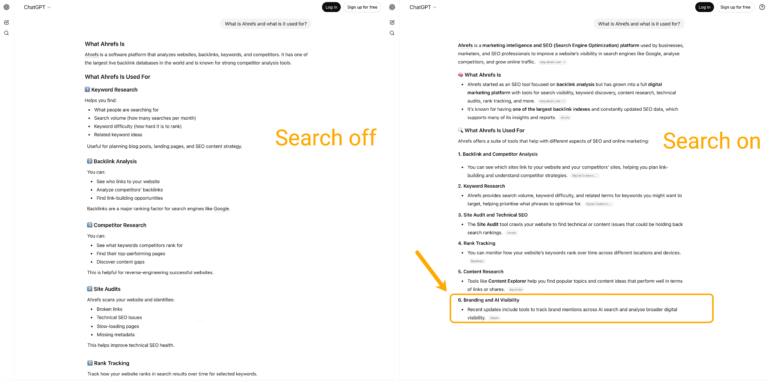
The core difference between hardware and software firewalls
The biggest difference is where filtering happens.
A hardware based firewall sits in front of the server and filters traffic at the network edge. A software firewall sits on the server and controls traffic there.
That difference affects:
- server resource usage
- rule management
- traffic handling capacity
- host level control
- scalability across servers
A hardware firewall is usually better when you want broader protection before the server is exposed. A software firewall is usually better when you want tighter control inside the server itself.
Performance and security impact on dedicated servers
A hardware firewall does not rely on the dedicated server’s CPU or memory to inspect traffic. That makes it a stronger fit when the server is already busy handling applications, databases, or high inbound traffic. It also helps keep performance more stable during spikes. From a security angle, it protects the network boundary first, filtering unwanted traffic before it reaches the operating system.
Its main advantages usually include:
- perimeter level protection
- centralized policy enforcement
- lower resource impact on the server
- better handling of heavier traffic
- easier control across multiple servers
A software firewall uses the server’s own resources. In many cases, that is fine. But as traffic volume rises, the impact becomes easier to notice, especially if the server is already under load. Its strength is that it gives control where workloads actually run, allowing traffic to be managed at OS and service level.
Its main advantages usually include:
- per server rule customization
- application and port level control
- simpler deployment
- lower upfront cost
- added protection behind other layers
Tip: If the server is meant for production traffic, ask whether filtering is handled upstream or on the host. That can affect both performance and protection more than expected.
Note: A software firewall is not a weaker option. It simply protects from a different layer, and it works best when server access rules are managed properly.
When to choose hardware, software, or both
A hardware firewall usually makes more sense when the server is internet facing, traffic levels are high, multiple dedicated servers need shared rules, or centralized control is important. For buyers planning long term infrastructure, this often provides a more stable foundation than relying only on host level filtering.
A software firewall usually makes more sense when the deployment is smaller, more customized, or more hands on. It is often the better fit when you are using one or a few dedicated servers, when each server needs its own access policies, or when cost efficiency and deployment speed matter more.
In many real deployments, the best answer is not one or the other. It is both.
A layered setup often works better because the two firewall types cover different parts of the same problem:
- hardware firewall filters traffic at the edge
- software firewall controls ports and services on the server
- both layers reduce reliance on a single control point
For dedicated server security, this is often the most practical model because it improves protection without depending on one layer alone.
What dedicated server buyers should look at first
Before deciding between a hardware based firewall vs software firewall model, it helps to look at a few practical points:
- how much traffic the server will handle
- whether the server is public facing
- whether you need centralized or per server control
- how much resource overhead is acceptable
- whether the setup may expand later
- who will maintain firewall policies over time
Those questions usually point to the right answer faster than comparing features in isolation.
How this fits into the server environment
A firewall should not be viewed on its own. Its value depends on the quality of the server environment behind it. Network routing, bandwidth quality, data center connectivity, and location all affect how well the security setup performs in practice.
For businesses using dedicated infrastructure in performance sensitive markets, it helps to work with a provider that offers a strong foundation. Dataplugs supports dedicated server deployments in key locations such as Hong Kong, giving businesses an infrastructure base where performance, security planning, and stability can work together.
Conclusion
Choosing between a hardware based firewall and a software firewall on dedicated servers comes down to where protection should happen and how the server will be used. Hardware firewalls are better suited to perimeter protection, centralized rule control, and higher traffic environments. Software firewalls are better suited to server level control, flexible deployment, and customized access policies.
For many dedicated server environments, the most effective approach is a layered one that uses both.
If you are reviewing dedicated server security as part of your infrastructure planning, Dataplugs can help you evaluate server options that align with your workload, traffic profile, and operational needs. You can contact the team via live chat or at sales@dataplugs.com to learn more about available solutions.